Unfortunately, no clever gadget can keep you entirely safe online
Since the revelations last year of widespread snooping into personal communications by US spying authorities, Silicon Valley has seen a wave of privacy-focused startups. Many of these companies have used Tor, the open-source network that allows users to browse the web anonymously by encrypting the data and then routing it scattershot through computers around the world.
Since the revelations last year of widespread snooping into personal communications by US spying authorities, Silicon Valley has seen a wave of privacy-focused startups. Many of these companies have used Tor, the open-source network that allows users to browse the web anonymously by encrypting the data and then routing it scattershot through computers around the world.
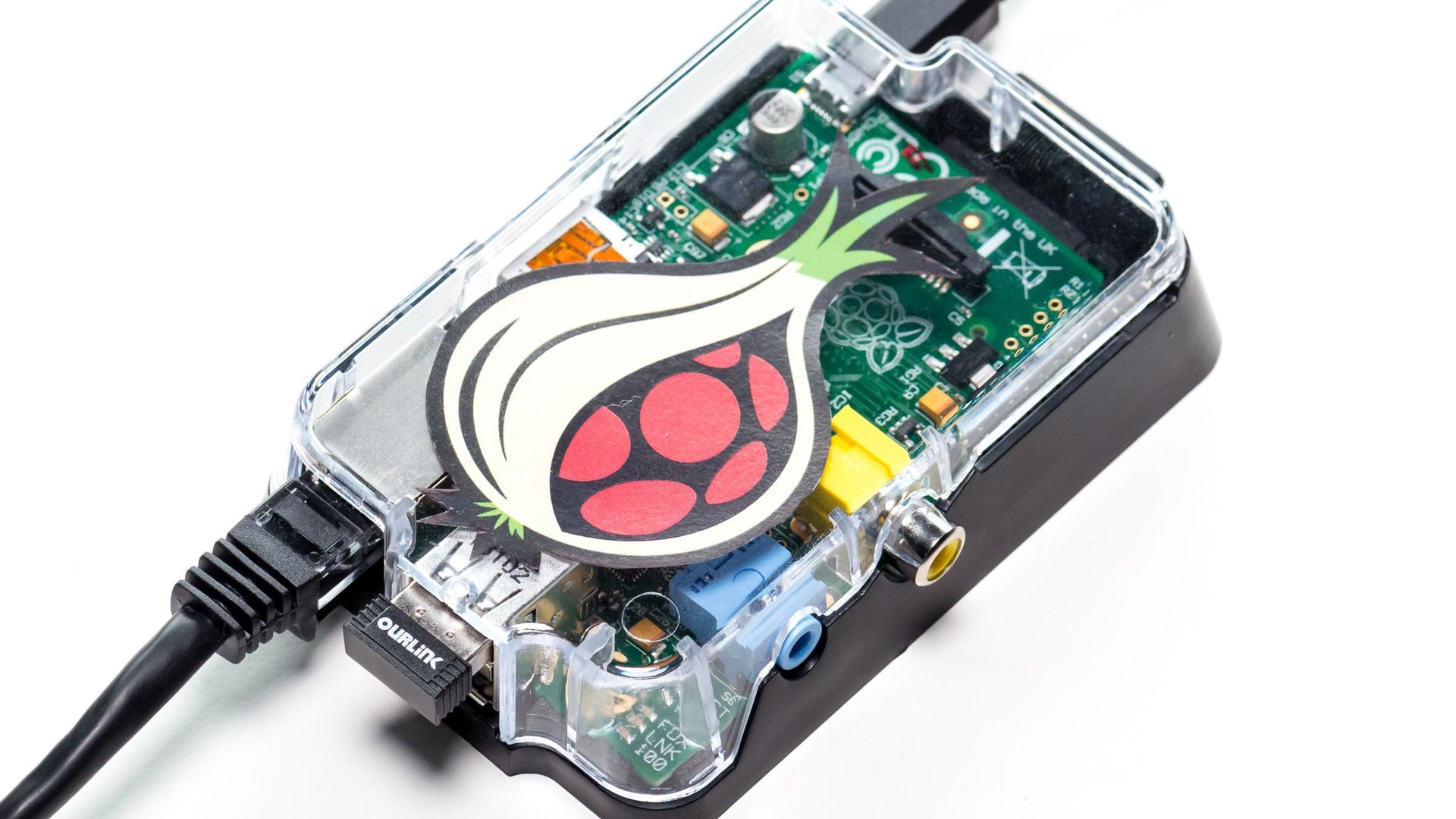
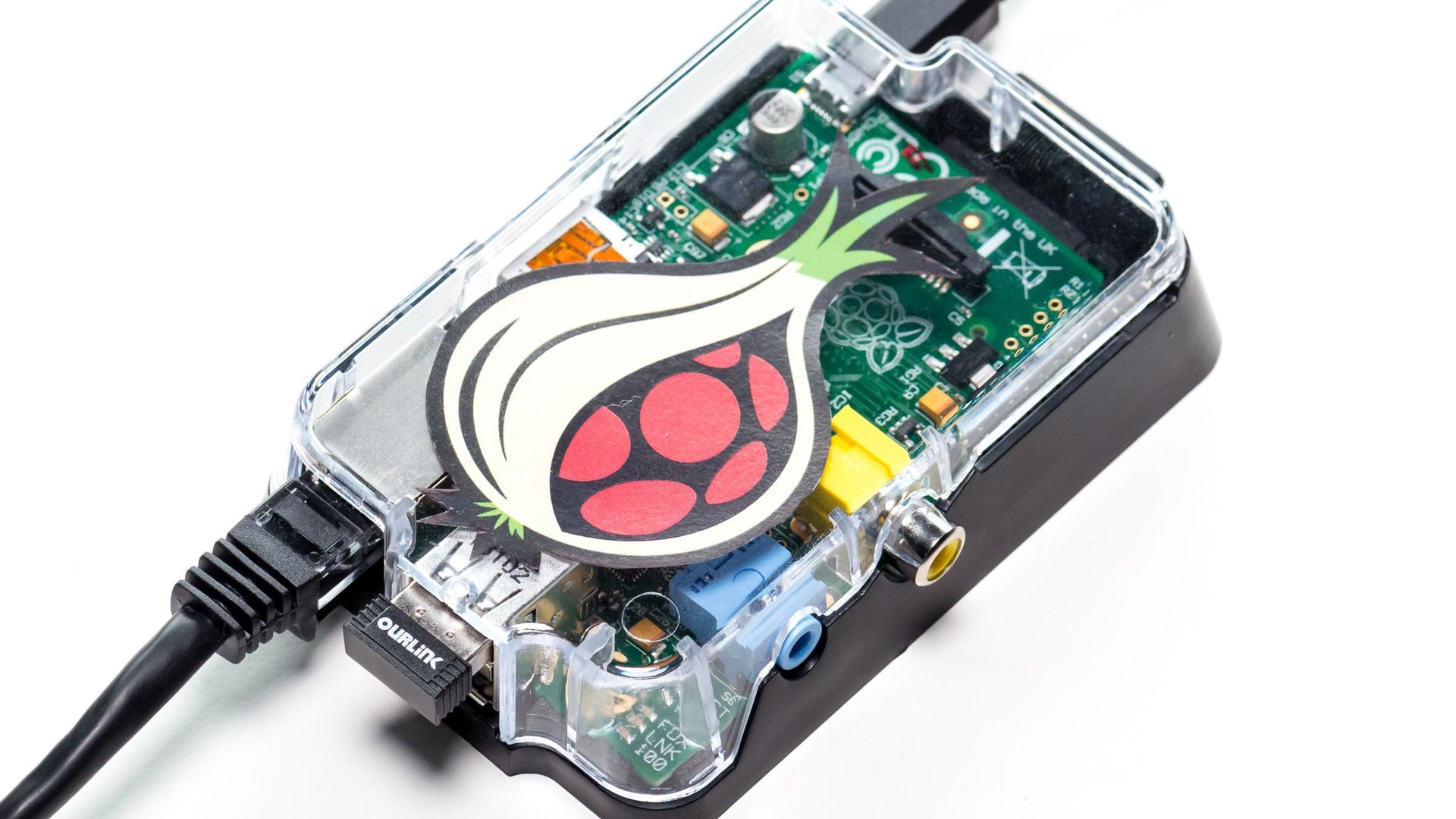
But to set up Tor on a computer requires a complex configuration that’s beyond most casual internet users. To solve that problem, a new generation of hardware that routes all communication through Tor has sprung up, acting like “a portable hardware condom on your ethernet cable,” in the words of Wired’s Andy Greenberg. These include Tor-sponsored projects such as Torouter and PORTAL, and independent startups such as OnionPi and Safeplug. These devices, however, have been criticized for their high costs, size, and security lapses.
The latest device soon to join the crowding market is called Anonabox, which has raised nearly $600,000 on Kickstarter in just a few days. Anonabox is a networking device based on open-source software that you can connect to either a home router, desktop, mobile phone, or tablet. The creators say it corrects the flaws of their competitors’ products with its low price (expected to be $45 at launch) and its small size (two can fit in a pack of cigarettes). According to its website, Anonabox’s founders got the idea for what they call an ”anti-censorship box” while watching the Arab Spring unfold, and they say the device’s small size makes it ideal for users in repressive regimes seeking to outsmart the authorities.

The backlash has begun
The critics are already out in full force. Anonabox developer August Germar hosted a Reddit Q&A discussion board on Tuesday and was lambasted by users who said his device suffered from the same flaws as those products already on the market. One user wrote that Anonabox’s hardware and software was not open-source and claimed that the product was essentially a copy of a Chinese-made router available for less than $20 on AliExpress, Alibaba’s bargain site. (Wired confirmed that the device was built using a stock hardware board and case, but quotes the developers saying that the hardware was modified.)
August Germar, one of Anonabox’s developers, vehemently denies that the product is a copy.
“People have said online that I just bought off-the-shelf Chinese hardware, used existing software and put on our logo—this is totally untrue,” Germar told Quartz. “We still had to write the software. What we’ve created is a new idea, an embedding network device that does encryption on the fly.”
Germar, who says he has already received requests for bulk orders from activists in Turkey and Hong Kong, did admit that he may have “misled” users to think that Anonabox custom-made the hardware, instead of ordering it from a manufacturer in China, where he says he has put in an initial order of 12,000 units. Besides, he says, the hardware itself is not the focus of Anonabox. Rather, the open-source software that powers the product is “our biggest selling point, and intended for developers to further innovate.”
Can hardware solve the privacy problem?
These issues aside, there are actually problems with the whole idea of privacy hardware, says Robert Neivert, a Silicon Valley-based privacy expert and founder of the data privacy firm Private.me. A physical gadget is unlikely to be able to keep up with changes in the Tor network itself, he tells Quartz. “It’s a piece of hardware, and when the standards and protocols for Tor software changes, it would likely stop working,” Neivert says.
After a security breach in Tor, he explains, Tor software engineers would release a “patch”—a process where the engineer applies a piece of code to the software to fix a specific problem. A hardware gadget such as Anonabox would likely not upgrade itself after any such breach in Tor’s software, and the patch would likely render hardware associated with the outdated software useless, said Neivert.
Germar confirms that Annonabox does not have the ability to upgrade itself after a breach, but says there’s an ongoing discussion internally and with some of the product’s Kickstarter following on how to tweak the first set of code to resolve this issue.
Anonymous browsing may miss the point
And even apart from security and the program’s technical viability, there are other issues with the whole idea of anonymity hardware, says Ross Anderson, a professor in security engineering at the University of Cambridge.
Though it may be helpful for activists in repressive regimes, there are actually some disadvantages for most people to remaining completely anonymous online, Anderson tells Quartz. For example, Anderson says, users routing their data through Tor would be limited in their ability to navigate sites such as Wikipedia or YouTube, which block anonymous users from certain content.
And ultimately, Neivert says, though Anonabox and similar products will likely correct their hardware issues, the whole idea of shielding a user’s identity online misses the point. For the kind of privacy issues that most internet users are concerned about—for example, identity theft and credit card fraud—anonymous browsing isn’t a silver bullet.
“Even if successful, these pieces of hardware are only addressing a 5% problem,” he says. “The 95% problem is that the websites themselves are being breached on an almost weekly basis…while Tor is good for protecting your communication online, it cannot prevent your credit card information from being stolen on Amazon.”
Update [5:35 pm ET]: Kickstarter has suspended this campaign, claiming that the project broke the site’s rules. More here.