A guide to staying online if the internet or social media gets blocked in your country
For digital rights activists, an important milestone came in 2016 with the adoption of the UN Human Rights Council resolution on promoting and protecting the freedom of users online. Yet, 51 intentional disruptions of the internet and electronic communications took place in the first 10 months of 2016 in countries across the world. For Africans, 2016 shaped up to be “the year of internet shutdowns,” as at least 11 governments interfered with the internet during elections or protests.
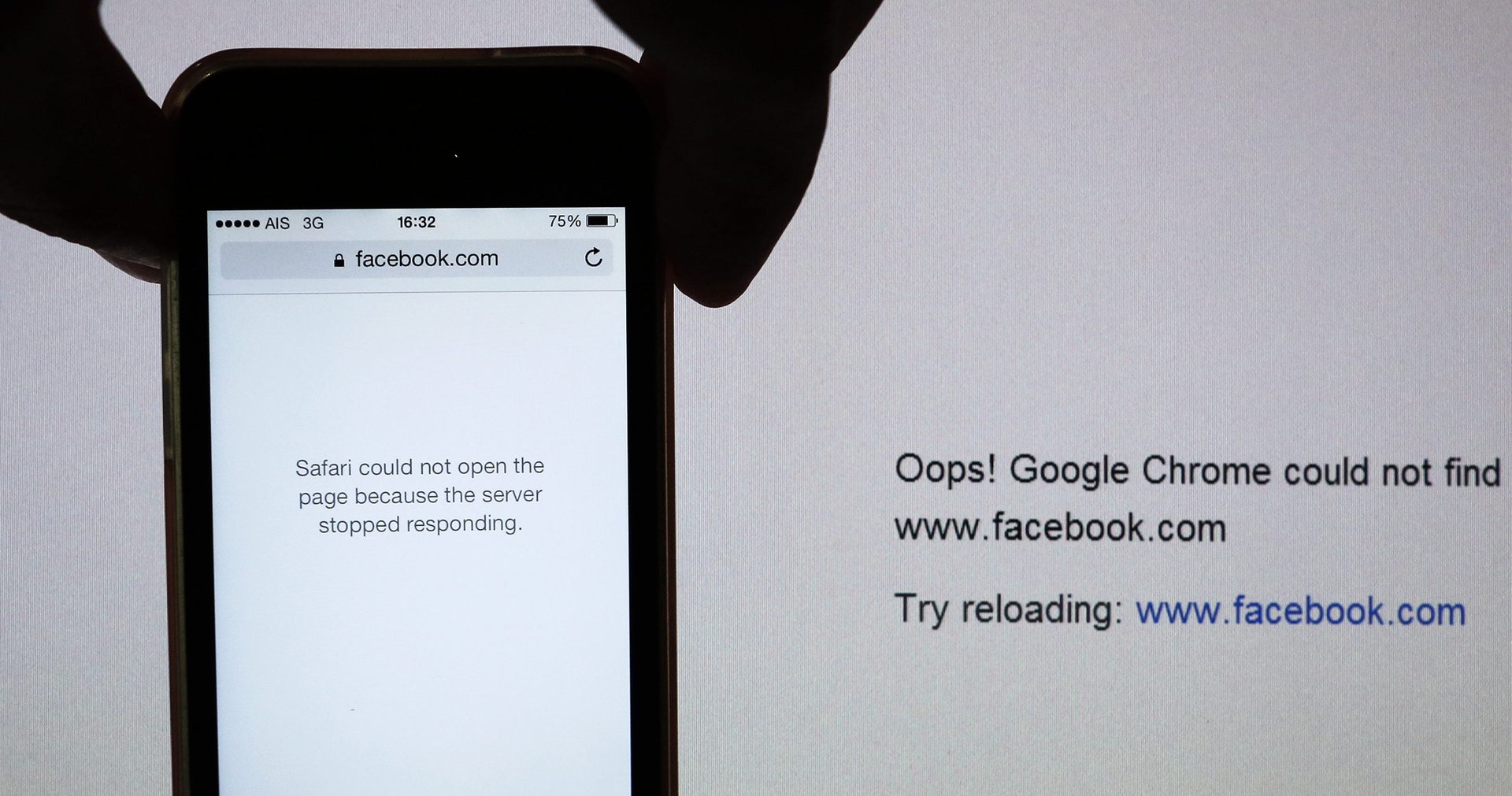
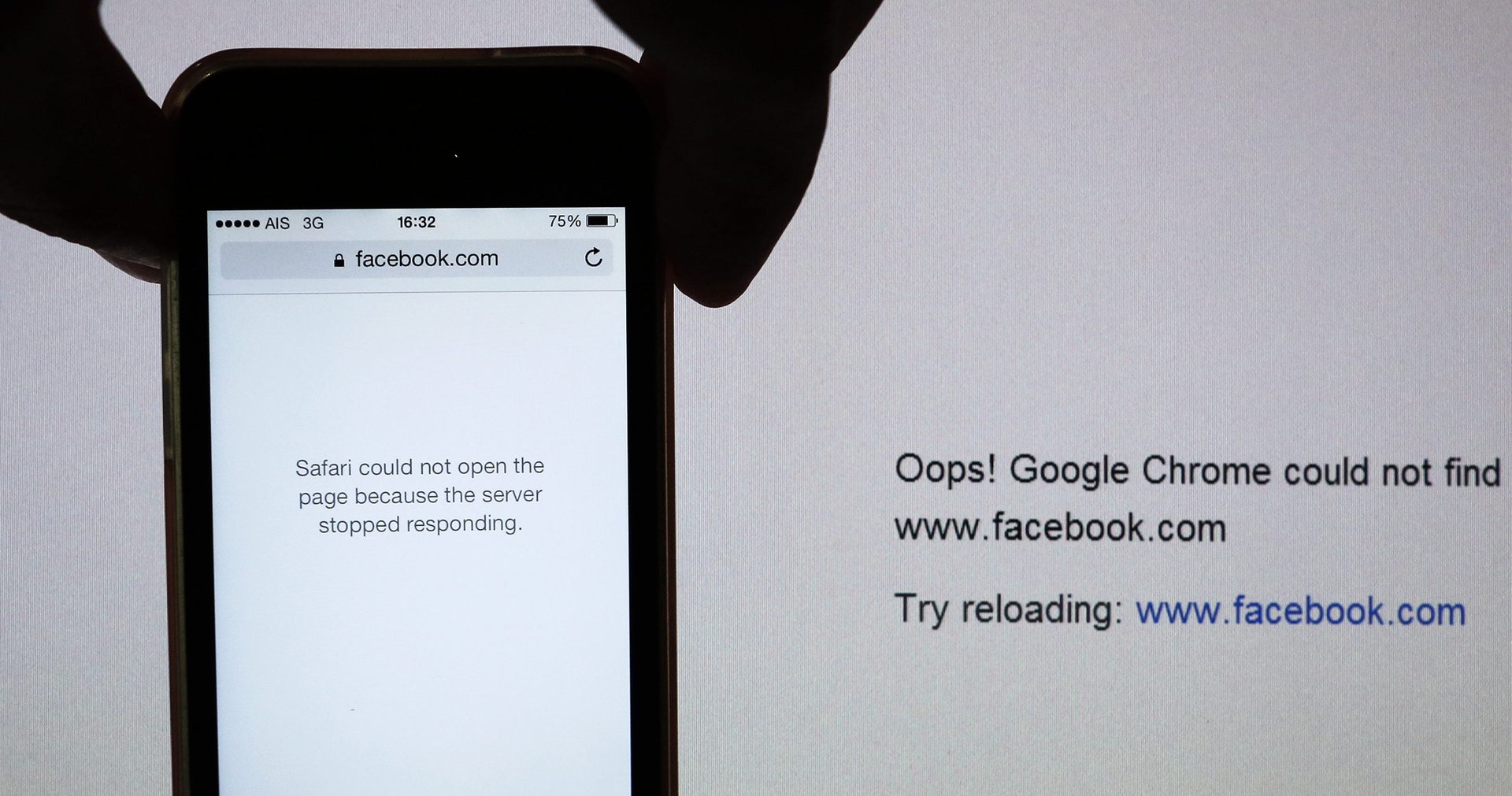
For digital rights activists, an important milestone came in 2016 with the adoption of the UN Human Rights Council resolution on promoting and protecting the freedom of users online. Yet, 51 intentional disruptions of the internet and electronic communications took place in the first 10 months of 2016 in countries across the world. For Africans, 2016 shaped up to be “the year of internet shutdowns,” as at least 11 governments interfered with the internet during elections or protests.
In 2017, the threat of internet blackouts, besides surveillance and monitoring of online activities, still looms large. Deji Olukotun, the senior global advocacy manager with Access Now says that there are significant challenges facing internet freedom. These include, he says, “the increasing sophistication of internet shutdowns to target smaller groups of people and locations” besides the deployment of technologies “that don’t truly provide new users with access to the full, open internet.”
Governments usually direct telecommunication companies to block certain websites or completely shut down the telephone and internet network. The next time that happens, here are a few things you can do to avoid the blackouts.
1. Learn which circumvention tools or proxies to use
There are numerous circumvention tools that can be used to evade censorship and to access the internet anonymously. These include Psiphon, an open source web proxy that helps users skirt content-filtering systems. There is also Tor, which essentially prevents people from tracing your location or spying on your browsing habits. Tor is available for Windows, Mac, Linux, and Android.
The Guardian Project also has a number of apps like Orbot that can help you browse the internet anonymously, send messages and encrypt your internet traffic. Tails is an operating system that enables you to start on any computer, allowing you to bypass censorship, and uses cryptographic tools to encrypt files and email messages.
Lantern uses peer-to-peer networks to get people in uncensored areas to share their Internet connection and servers with those without the same unfiltered level of access. Peer networking is also used with FireChat, an off-the-grid messaging app that allowed users to chat using Bluetooth or wireless during blackouts in Iraq, Iran, and Hong Kong.
But beware: governments can sometimes use sophisticated technology to block these same sites or introduce jail terms for using them. A 2016 Amnesty International report showed that the Ethiopian government blocked both Tor and Psiphon during anti-government protests there last year.
2. Ensure the safety of your VPN
Many people use virtual private networks, or VPNs, to get secure access to a remote computer over the internet. For instance, VPNs constituted the top 12 apps downloaded during Uganda’s elections last February. VPNs can, however, differ from region to region, and it is important to know the safety and security of each specific networks before use. Access Now recommends That One Privacy Site as a source that compares different virtual networks.
Amama Mbabazi, a presidential candidate in Uganda’s 2016 elections referred his followers to the Tunnelbear VPN.
3. Remember to protect yourself
Trying to circumvent an official shutdown to get online is weighty task—but it all starts with the simple stuff. For instance, ensure that all the sites you are using are delivered over HTTPS. This allows you to access the original site and not an altered version of it. Quartz recently switched to HTTPS to make it secure for readers to browse our journalism. You can install the HTTPS Everywhere extension in your browser courtesy of the Electronic Frontier Foundation and the Tor Project.
Another important thing to have is anti-virus software, so as to detect and remove malicious software from your laptop. “Something as simple and as basic as having an anti-virus is a key thing. People don’t know much about this,” Ephraim Muchemi, who conducts training in digital security with the US-based non-profit International Research and Exchange Board.
4. Seek help from the experts
For journalists and writers who are engaged in reporting sensitive information, it is important to know where to seek help before blackouts. Access Now, for example, runs a 24-Hour Digital Security Helpline, which can advise users even during emergencies. Reading their Digital Security Booklet can be a key place to start.