Say you wanted to send an email more secure than any message that had ever been transmitted in human history, a message with absolutely no chance of being intercepted. How would you do it?
You may have encrypted your message according to the highest standards, but encryption doesn’t guarantee secrecy. The fact that you sent it is still detectable. An intercepting party in possession of just a few clues such as your identity, the receiver’s identify, the time of the message, surrounding incidents and the like can infer a great deal about the content of the message in the same way that the NSA can use your metadata to make inferences about your personality. You need to conceal not just what’s in the message but its very existence.
The answer? Make your message literally impossible to detect. A team of researchers from the University of Massachusetts at Amherst and Raytheon BBN Technologies led by Boulat A. Bash have created a method for doing just that, cloaking electronic communications so that the communication can’t be seen. They explain it in a paper titled Covert Optical Communication.
The question of exactly how secure any communication can be is of no small relevance either to national security watchers worried about losing secrets or to a public increasingly concerned about governmental invasion of digital privacy. The breakthrough shows that it is possible to send a message that can’t be intercepted, no matter how determined the National Security Agency is to intercept it.
The practice of embedding secret messages in computer files is called digital steganography. Steganography has been around since the days of ancient Greece. The term simply refers to the deliberate hiding of a message within a message. Dissidents in Laos, the United Arab Emirates, Saudi Arabia and especially China use digital steganography to send secret messages. But these methods are far from fully secure.
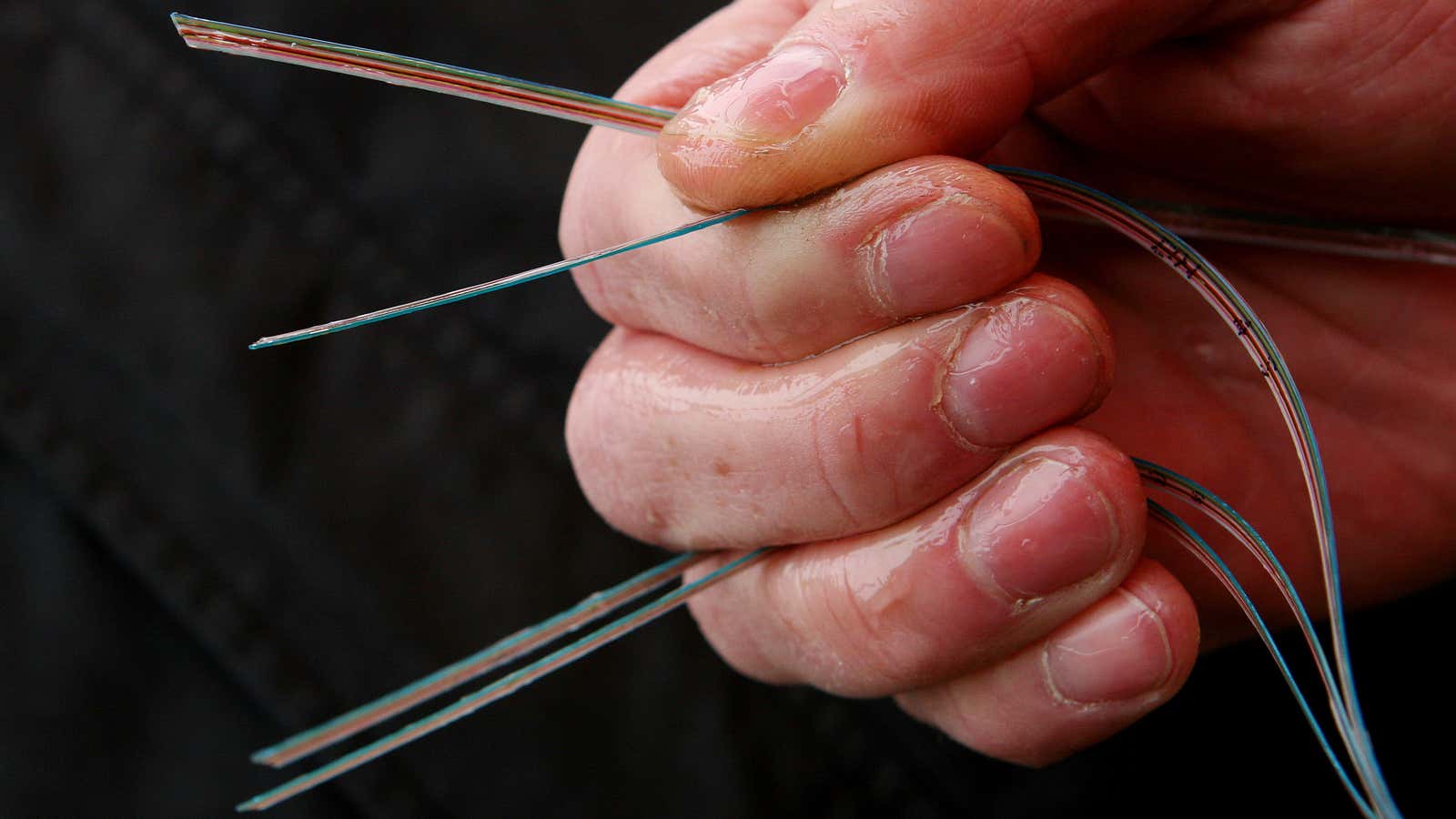
Today, we send a lot of messages over fiber-optic cable, essentially using light as a communications medium. It’s instant and cheap but someone monitoring the photons passing through those cables can detect when one party is sending a message to another (it is just light, after all.) Photon detectors are extremely accurate, able to detect single photons passing between two points, but they aren’t perfect and sometimes they read false positives. Bash’s technique makes use of that flaw using pulse position modulation—and it’s not much more complicated than Morse code.
Take a unit of time, like a second, and chop it up into smaller parts that vary in size, one-fourth, one-eighth, etc. Then assign each band a corresponding symbol. There’s your code. You can transfer a photon-based message over a fiber-optic capable that corresponds to the code and—so long as the message sender and the receiver of the message both have the key to the code—then each can read the message.
Pulse position modulation is not new. The formula that Bash and his colleagues created takes this process to the next step rendering it far more useful. It solves for how many bits of message a sender can pack into a certain interval of time in order for the message to always appear like background noise to any detector currently in existence.
In addition to light-based communication, the formula would render undetectable cell phone-based text messages. Cell phones use microwaves to send and receive data, which is a very noisy area of the electromagnetic spectrum. More noise is good in Bash’s communication-concealing scheme in the same way that it’s easier to hide in dense jungle foliage than it is in open desert.
Unfortunately, you and the person you are sharing the message with must agree in advance on the code and exchange it, which presents something of an obstacle.
While there is no way to share a secret code in an invisible email, there is a way to share it in an encrypted email that would destroy itself if viewed by an outsider. Using quantum encryption, you could send a message between two parties containing the deciphering key and that message, while detectable, would also be unhackable.
University of Oxford quantum physicist Artur Ekert calls quantum encryption the ultimate physical limits of privacy. Other key distribution schemes such as the Diffie Hellman scheme, rely on the difficulty of mathematical problems to work, whereas quantum encryption does not. According to Heisenberg’s uncertainty principle, objects viewed on the atomically small quantum scale change their behavior when viewed. Quantum encryption offers the possibility of a message so secure that any attempt to read it without authorization will destroy it, not because of some programmer’s whim but because of the way subatomic particles operate.
“For quantum cryptography we need ‘only’ to transit quantum particles over a certain distance, and this is relatively easy. Quantum cryptography has been demonstrated in practice and there are even companies that can sell it to you,” Ekert told Defense One.
Quantum cryptography and Bash’s pulse position modulation technique are two very different animals. Cryptography makes messages difficult to decipher and pulse position modulation cloaks them so that they can’t be detected. But Bash’s method could go hand-in-hand with something like quantum key distribution, which a message sender would use in advance to share the key code. That, in turn, would be used in the future for covert communication.
Here’s what the most secure electronic message exchange in the history of humanity would like: You would first exchange the code key in a quantum encrypted message, and then, when the receiver and the sender both had the code, they could exchange an invisible—thus perfectly secure—message. A third party might be able to detect that two parties had exchanged a single message that had been quantum encrypted, containing the key code, but that third party wouldn’t be able to see any of the exchanges that passed after that or open the key code message.
Right now, quantum encryption is not the sort of service you can use on your iPhone or some common device. It requires dedicated devices and a connection between two points. But that will change, according to Ekert. “We will probably demonstrate device independent quantum crypto soon in the labs, but it will take some time before we turn them into a commercial proposition,” he said.
How soon? Perhaps sooner than many think. Back in August, members of a team from the University of Bristol published a paper outlining ideas for how to do it.
Secure? Yes. Practical for all communication? No. Bash’s method is not one you would use for everything. The laws of physics that make photon cloaking possible impose a stingy limit on the size of the message that is transferable over that medium, limited to tens to hundreds of bits of per second according their paper. That’s enough space to send yes or no signals or small values, but sending an entire Word document at that rate would take a very long time.
The NSA is spending nearly $80 million on a program called Penetrating Hard Targets to build a quantum computer to de-encrypt the most expertly encoded communications, according to The Washington Post. The government has been funding quantum computer research for more than a decade to develop techniques for super hacking. So far, the record suggests that they have little to show for their efforts.
“Purely on numbers, the agency would appear to be lagging behind major labs such as the Institute for Experimental Physics at the University of Innsbruck in Austria,” noted Jon Cartwright in a recent piece for Physics World.
Despite the agency’s reputation for digital omnipresence, their real capabilities are far from godlike.
“The recent Snowden revelations confirm something we’ve long suspected: NSA does not really have a supercomputer that can break all of our standard cryptography. What they’ve resorted to is colluding with equipment manufacturers to include ‘back doors’ in encryption products and software,” Johns Hopkins University cryptology expert Matthew Green toldDefense One, referring to the recent revelations that the NSA had given security industry provider RSA multiple encryption tools. “All of this discussion about quantum crypto is moot if someone puts a back door into the hardware responsible for performing the encryption.”
For the majority of the public, the best way to secure your personal email is to use some commonly available tools, Green said.
“Our current practical encryption schemes are all extremely secure, and there’s no reason to believe that your communications aren’t confidential—provided you’re using encryption and it’s properly implemented,” he said. “In theory, these schemes can be broken, but the computational effort to do it is far beyond what humans will ever muster.”
This post originally appeared at Defense One. More from our sister site:
Congress wants Obamacare exemption to help boost veteran employment