It’s not just your credit-card information that hackers want—it’s your medical records, too. To prevent cyberattacks from taking down hospital systems and infecting life-saving machines, the same blockchains used to decentralize cryptocurrencies like bitcoin and ethereum could be used to safeguard patients both past and present.
The WannaCry cyberattack was a wakeup call for healthcare providers. On May 12, supercharged by a cyber weapon developed by the National Security Agency, WannaCry’s ransomware spread across the world, infecting as many as 300,000 computer systems in 150 countries, including at 48 hospital trusts in the UK. The attack, which forced many hospitals to cancel or delay treatment, is a warning to the healthcare industry: Patient care can be compromised, even causing terminal danger, if computer systems suffer a security breach. For example, the US Food and Drug Administration warned in January 2017 that implanted heart devices made by St. Jude Medical were vulnerable to computer hacking. A cyberattack of this nature could cause the lifesaving device to rapidly deplete its battery.
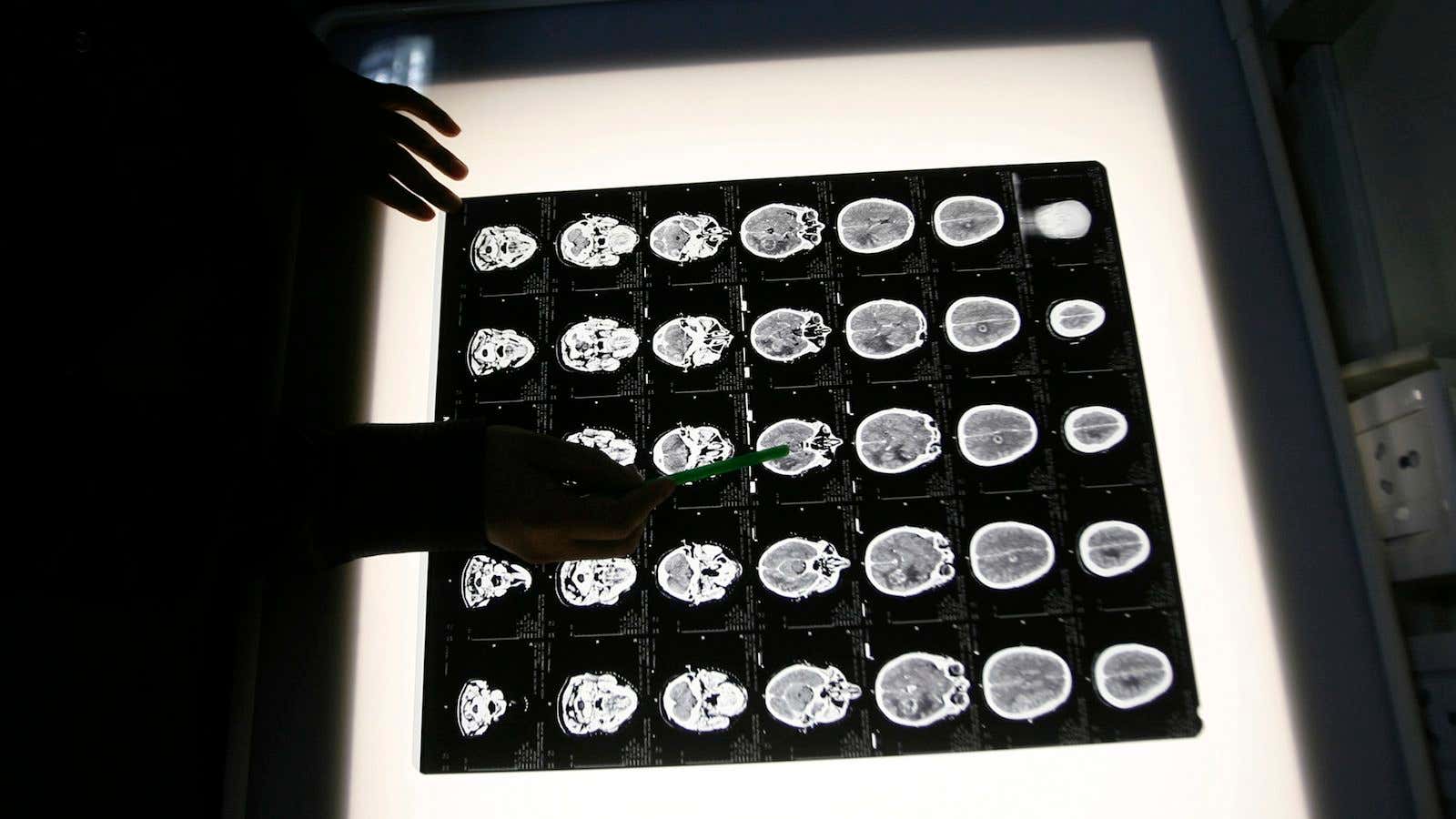
Many people don’t realize that hospital hardware such as MRI and x-ray machines are computers, which means their software can become vulnerable to cyberattacks. It doesn’t help that many hospitals’ machines are old and their software outdated; a report published in 2016 by Motherboard found that many UK hospitals’ antiquated software does not receive security updates. Microsoft issued a patch for the software that could be compromised by WannaCry, but such reactive security measures are often too little, too late. The focus must shift away from reaction to prevention and real-time management, and that starts with endpoint security on all medical devices.
Many devices in hospitals often do not use traditional security mechanisms because they do not have enough memory or processing power. It is also more challenging to install security updates because the devices are often connected to a local area network. With a LAN, hospitals must either enable internet access to download updates or try to push updates from the local IT server, which requires training and infrastructure that most hospitals do not have.
By using a distributed, permanent digital ledger to disseminate updates—such as a blockchain, the technology that underlies cryptocurrencies like bitcoin—medical devices can update security software directly. Blockchains generally require a large memory footprint, but it is possible to compress a blockchain to fit onto small endpoint devices. Disseminating security updates such as malware signatures and intruder addresses can equip endpoints to handle emergent threats.
The blockchain has many more applications in helping to prevent damaging cyberattacks on critical healthcare infrastructure. There is a strong solution in running all communications through the blockchain, which does away with the traditional server/client paradigm, and which has no single point of failure. As the blockchain is pseudonymous, it also prevents an entire hospital network being breached if a hacker gains access to a single medical device.
One of its key characteristics is immutability. The use of sequential hashing, cryptography, and its decentralized structure make it near impossible to unilaterally alter data. A hacker would need to take control of more than 51% of the processing power of the blockchain to change the ledger—a difficult feat. Healthcare providers who routinely handle sensitive data can use the blockchain as a communication protocol to deliver security updates to otherwise vulnerable endpoint devices.
Another problem faced by hospitals is that in the era of on-demand cloud services, data needs to be accessed by multiple parties. The blockchain can secure communication protocols by requiring dual-factor identification: Someone wishing to access data must enter a pin, which must be reconfirmed across the blockchain before they are granted access to data. This not only prevents data from being meddled with, but also stops it from falling into the wrong hands.
There is no silver-bullet solution to combatting cybercrime in healthcare—but the blockchain can improve endpoint security make systems more secure in the face of the cyberattacks.